
Brought to you by Parallels
One of the biggest bugbears about running a connected business today is the growing menace of cyber attacks. Every new piece of software that is rolled out should rightly be scrutinised for potential vulnerabilities.
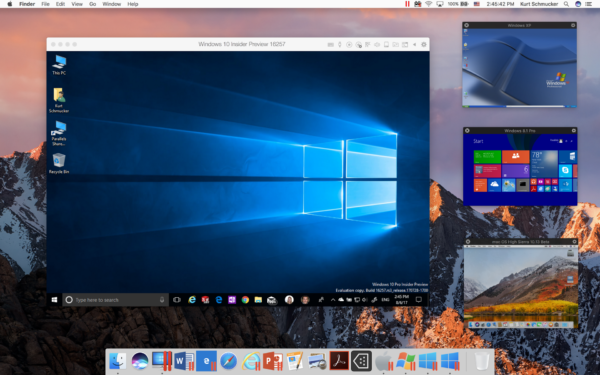
Some businesses have taken the approach of deploying Apple Mac devices, thinking that it’s an inherently safer alternative to Windows-based PCs. Some even go one step further and decide to run Windows in a virtualised sandbox via Parallels Desktop for Mac.
Indeed, when businesses deploy Parallels Desktop in the enterprise, they can rest assured that it is designed to address users’ most pressing security concerns. It has safeguards built in to keep out various threats that could potentially impact the enterprise.
All these measures do not mean everything is fail-safe, of course. Nothing is, so let’s get down to answering some common questions on running Windows on a Mac with the latest Parallels Desktop 13.
Firstly, can you get a virus from running Windows on a Mac? The version of Windows you install via Parallels Desktop 13 is a full-fledged one, so it comes with both the strengths and weaknesses of the operating system. So, the answer, unfortunately, is yes. You can have Windows files infected by malware, just like any other PC.
To counter this, one way is to have the antivirus option turned on for the Windows virtual machine (VM). Keeping a watchful eye over the Windows OS and scanning the files like what other PC users do, will reduce the threat greatly.
Secondly, can the Mac OS files be infected by a virus from Windows? Since malware is usually written to exploit specific vulnerabilities, it is unlikely it will have the capabilities to affect both operating systems.
It is important to note the separation of roles in Parallels Desktop 13. Although users can easily drag and drop files from a macOS screen to a Windows screen, there are measures in place to separate the two operating systems in key areas.
Like other macOS processes, the Windows VM application is restricted in terms of virtual memory space isolation and macOS file permissions. As a user-mode app, it cannot access arbitrary files, memory segments or processes in a host OS.
To be sure, a malware could conceivably access files in a folder shared by Windows and macOS, but it cannot alter important system files. If this is a concern, this shared-file feature can be turned off by an administrator as well.
Supporting a network of users with different needs often means being flexible with the VMs they run to access the apps they need. A school, for example, may require students to run both Mac and Windows apps.
For administrators, what is needed are robust tools to ensure that security is at the core of such a setup. Key to this is the ability to restrict access to key components of the VM setup.
In Parallels Desktop 13, a local system administrator’s password can be made mandatory before key changes are made, such as the removal or cloning of a VM. This helps prevent the loss or theft of data.
VMs can also be locked to prevent configuration changes. With Parallels Desktop Business Edition, a system administrator can assign a password to lock up individual VMs.
What if you need to back up a VM? Convenience should not be at the expense of security. While Parallels Desktop allows VMs to be automatically backed up, so they can be rolled back easily, these backup images can be protected using 128-bit AES-CBC encryption.
This way, a user must enter a valid password to open and start an encrypted VM. Administrators can also use an external third-party dynamic encryption library should they prefer.
Built into Parallels Desktop, these features make life a lot easier for administrators seeking to support users in a mixed OS environment. Robust yet accessible, they empower users while ensuring that security is baked in by design.
It also helps that Parallels Desktop Business Edition comes with the capability to mass deploy and manage Parallels Desktop installations and Windows VMs.
Besides bringing the best of both Mac and Windows to users, administrators can now have a better view of the devices in the corporate network. No longer do they have to manually access each device to ensure things are running smoothly and securely.






