Brought to you by Keysight Technologies
By Sook Hua Wong
IoT deployment is happening rapidly. According to IoT Analytics, the number of connected devices in 2019 is expected to surpass initial forecasts by 14 percent to reach 9.5 billion. The three main drivers are explosive growth of consumer devices, much stronger than expected cellular IoT/M2M connections, and strong device connectivity growth in China due to government initiatives.
This exponential growth rate is expected to continue for the next few years to reach 28 billon connected devices by 2025. Technology is already integrated into our wearables and clothes. There will be 26 smart objects for every human being on earth. 75 percent of cars will ship with necessary hardware to connect to the Internet. Healthcare-related IoT revenues are predicted to increase to over US$135 billion by 2025.
IoT deployment is diversifying from consumer-based applications such as smart home devices and wearables to mission-critical applications in the areas of public safety, emergency response, industrial automation, autonomous vehicles and Internet of Medical Things (IoMT).
Mission-critical applications make use of the convenience, low costs, and long battery life of IoT devices as well as widely available public infrastructure to improve interoperability and interconnectivity between devices to allow real time monitoring and control of various critical devices and systems.
As these mission-critical applications proliferate, the IoT devices and systems need to be robust to withstand the rigors of the real world.
Great potential comes with great challenges
IoT brings benefits to consumers and creates new business opportunities for commercial applications. However, these require stable and reliable hardware and infrastructure.
Emergency response system: Imagine what will happen if the wireless sensor that monitors the pressure of a remote gas pipe crashes due to previous power outages? During an emergency, the piping system can explode due to lack of timely action to contain it.
Digital health: Remote patient monitoring devices enables monitoring of the patient outside of conventional clinical settings, which enhances patient access to care and decreases healthcare delivery cost. However, the device itself needs to work in any environment such as in a crowded stadium or in a hard to reach underground warehouse. Signal reception through concrete structures and interference from surrounding devices should not impact the normal operations of the monitoring device.
Smart meter: With hundreds of thousands of tiny smart meters deployed in every remote location, these meters need to work seamlessly to collect and transmit utility data. Any failure to the smart meter will result in errors in consumption tracking, causing revenue loses and potentially ruining the reputation of the utility companies.
Connected car: A connected car, such as in Figure 1, brings tremendous conveniences to us. But it also exposes us to various risks. Security flaws in wireless system implementation could allow a hacker to locate and hijack our car with just a push of a button without us noticing.

Engineers and designers working on these mission-critical systems or devices face intense technical challenges and must make important design and test considerations and tradeoffs from the early design phase to the end of manufacturing.
Addressing technical challenges through the 5Cs of IoT
A comprehensive approach is required to address the multi-faceted technical challenges in IoT devices and systems throughout the entire product lifecycle. As shown in Figure 2, the design considerations can be summarized based on the 5Cs of IoT.

1. Connectivity
Connectivity is about the ability to enable seamless flow of information to and from the device, infrastructure, cloud and applications.
Achieving good connectivity is one of the top challenges faced by engineers because the wireless connectivity system is highly complex, and dense device deployments further complicate operations.
Mission-critical IoT devices are expected to work reliably without failure even in the toughest environment. The fast-evolving wireless standards add to the complexity and engineers face constant challenges to keep pace with the latest technologies and ensure devices can work seamlessly throughout the ecosystem.
Responding to connectivity challenges require the careful selection of design and test solutions that are highly flexible, configurable and upgradable to meet future needs.
The solution needs to be highly flexible to test devices with many radio formats, able to access device performance under actual operation modes, and support over-the-air testing in signaling mode without the need of chipset specific driver.
Preferably, the system should also be simple, inexpensive, and can be used in both R&D and manufacturing for code leverages and to minimize measurement correlation issues across the different phases of development.
The demand for IoT devices will increase exponentially due to their rapid proliferation. Manufacturers need to have a highly scalable, cost-effective and reliable manufacturing test system that can easily meet the increasing volume while ensuring device quality.
2. Continuity
Continuity is about ensuring and extending the battery life of the device. Battery life is one of the most important considerations for IoT devices. Long battery life is a huge competitive advantage in consumer IoT devices.
For industrial IoT devices, a battery life of five or ten years is the common expectation. For medical devices, such as pacemakers, device life can mean the difference between life and death. Battery failure is not an option.
To meet this long battery life requirement, the integrated circuit (IC) designers need to design ICs with deep sleep modes that consume very little current, reduce the clock speed and instruction sets, as well as implement low battery voltages.
From a wireless communication perspective, standard groups are also defining new low power consumption operating modes such as NB-IoT, LTE-M, LoRa, Sigfox that offer limited active operation time while maintaining low power consumption.
Product designers who integrate sensing, processing, control and communication components into the final product, must know how the peripherals behave and consume power, and optimize the product’s firmware and software to simplify operation and reduce power consumption. All these activities require capable measurement tools that can offer deep insights into the device current consumption behaviors.
3. Compliance
Compliance is about making sure your IoT devices adhere to the radio standards and global regulatory requirements before gaining market entry.
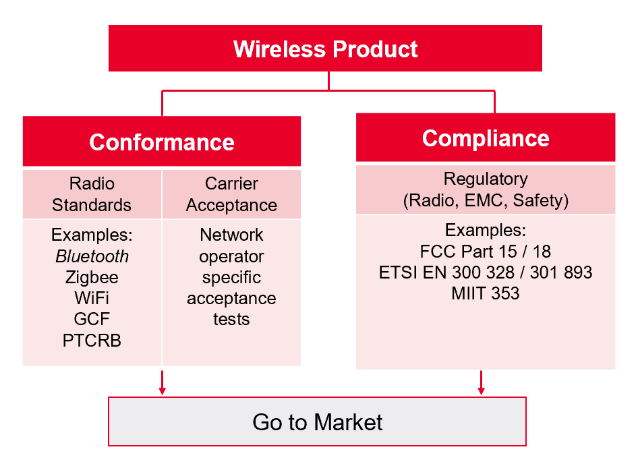
There are two main categories of compliance tests: radio standards conformance and carrier acceptance tests, and regulatory compliance tests such as RF, EMC, and SAR tests.
Design engineers often scramble to meet the tight product introduction timeline and ensure smooth global market penetration while complying to the latest regulations.
Frequent updates to the regulations also further add to the complexity. Figure 3 shows the examples of conformance and compliance testing requirements.
To reduce the risk of failure during compliance testing and to keep to the product release schedule, designers can consider investing in inhouse pre-compliance test solutions so that testing can be carried out at every stage of design to fix issues early in the design phase.
Choosing a pre-compliance test system that is adapted from the compliance test system from the test lab can also help to ensure measurement correlation and reduce risk of failures.
Compliance testing is complex and time-consuming. It can take up to days or weeks to complete if performed manually. Choosing an automated test system can help to save test time and allow faster time-to-market.
4) Coexistence
Coexistence is about the ability of the wireless device to operate reliably in the presence of other interfering signals. With billions of devices released to the market, congestion in the radio channels is a problem that will only get worse each day.
To address wireless congestion, standard bodies have developed test methodologies to evaluate device operations in the presence of other signals.
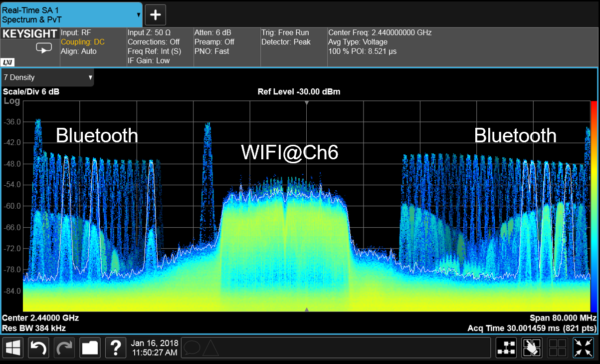
For instance, in Bluetooth®, adaptive frequency hopping (AFH) lets a Bluetooth device drop channels that experience high data collisions (figure 4).
There are also other collision avoidance techniques such as listen before talk (LBT) and cooperative collision avoidance (CCA) to improve transmission effectiveness. The effectiveness in a mixed signal environment is unknown. When the radio formats don’t detect each other, collisions and data loss will happen.
For consumer applications, delays or pauses in wireless headsets or wearables are annoying, but acceptable. An industrial sensor that loses the control signal, or an infusion pump that stops working due to surrounding interference signal can have dire consequences.
Therefore, it is crucial to perform coexistence testing to measure and assess how your device will operate in a crowded and mixed signal environment.
IEEE provides some guidance in ANSI C63.27 (American National Standard for Evaluation of Wireless Coexistence) regarding key considerations for coexistence testing that includes evaluation processes, test setups and risk-based testing tiers.
Device manufacturers are highly recommended to assess the potential risk to maintain the device’s functional wireless performance in the presence of unintended signals found in the same operating environment.
5) Cybersecurity
With increasing deployment of IoT in mission-critical applications, the need for cybersecurity protection is becoming even more important. While cyberattacks can happen at many layers – from the device level to the communication network, cloud or applications, most of the traditional security protection tools have focused on securing the network and cloud.
The endpoint and over-the-air vulnerabilities are frequently overlooked. Formats like Bluetooth and WLAN are matured technologies and are commonly used in many applications. However, little has been done to address the over-the-air vulnerabilities.
The complexity of these wireless protocols translates into potential unknown pitfalls in the device radio implementations that allow hackers to access or take control the device.
According to IDC, 70 percent of security breaches originate from endpoints. Extra care should be taken to safeguard these IoT devices. Over-the-air vulnerabilities and potential point of entries into the IoT devices should be identified.
The device should be tested using a database of known over-the-air threats/attacks to monitor the device response and to detect anomalies. The database must be regularly updated to safeguard the device from the latest threats.
Building a strong foundation through the 5Cs of IoT
IoT opens doors to exciting new applications and opportunities for many industries. But it also brings unprecedented challenges that require thinking in new ways to meet the mission-critical requirements.
Delivering successful IoT implementation requires designers and engineers to overcome the technical challenges in the 5Cs of IoT.
Having a deep understanding of these technical challenges and knowing what the key design and test considerations will build a strong foundation for implementation and deployment across the IoT ecosystem.
The right design, validation, compliance testing and manufacturing tools throughout the product lifecycle will help to ensure that the IoT delivers on its promises.
Sook Hua Wong is industry segment manager for General Electronics Measurement Solutions at Keysight Technologies.






