Brought to you by Sophos
One thing 2017 will be remembered for is how ransomware realised many long-held fears of a cyber attack. Spreading fast to hundreds of thousands of computers across the globe, malicious code found easy victims from hospitals to nuclear plants, like never before.
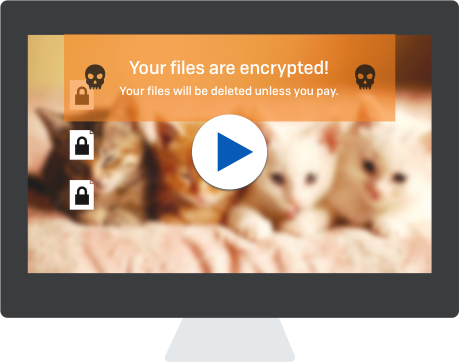
On their screens, those affected were told to pay up in Bitcoin or forever have their files encrypted and locked from them. Even if these could be restored, the operation often took up valuable time and resources.
The WannaCry ransomware, launched in May this year, reached more than 230,000 computers in more than 150 countries. Just a month later, the followup Petya disrupted anything from ATM machines in Ukraine to a chocolate factory in Australia.
The widespread impact is a reminder that cyber threats; worms in particular, are aimed at finding as many vulnerable victims as quickly as possible, affecting organisations big and small. In an interconnected world, anyone can end up being a target.
The attacks also shine a light on the new methods employed by cyber criminals. Unlike in previous years, they do not need highly-skilled hackers to mount a lucrative ransomware attack.
Instead of looking for software exploits, then designing the attack and setting up a server to collect the ransom, they look to an established ecosystem to give them all the tools. This underground economy has been dubbed ransomware-as-a-service, a play on the idea of on-demand services delivered over the cloud.
On the Dark Web, a cyber criminal can download an easy-to-use tool that compiles and prepares the malware to be loaded onto a victim’s computer. He can select how he delivers the payload, say, via a Word document or e-mail.
He can customise what files to encrypt and lock out, then set the ransom to be paid. He can even select which countries to target. Usually they are rich ones where victims can cough up the ransom.
With the payload ready, the cyber criminal next looks for a freelance writer to craft a fake e-mail to lure people into clicking a link or opening an infected file that installs the malware on their PCs. To make things more realistic, he may even find a translator to make sure the messages make sense to victims from different regions.
According to SophosLabs, there is a growing trend among cybercriminals to craft customised threats using vernacular languages, brands and payment methods for better cultural compatibility. To be highly clickable and as effective as possible, these threats now impersonate local postal companies, tax and law enforcement agencies and utility firms, including speeding tickets and electricity bills.
Of late, law enforcement agencies have taken down some Dark Web marketplaces that trade in such ransomware services. In June, American and European authorities shut down two marketplaces where illegal goods such as malware, weapons, drugs and stolen identities are sold.
However, the cat and mouse game is expected to go on, as long as there are illegal items to be traded at prices that are attractive. Ransomware-as-a-service is one such item.
How can enterprises get smarter to avoid being an easy victim? The first thing to do, as always, is to have a ready backup of the most important files. Even if a computer gets hacked or encrypted, the backup can help restore things back to the state before the attack.
However, this manual way of cleaning up takes valuable time, requiring down-time to a business. In some cases, this can take days or even weeks to complete.
As the bad guys fine-tune their attacks, should enterprises get smarter with their defences? They cannot simply rely on a tool that uses malware signatures to detect if something is wrong, because there is a lot of malware that doesn’t get recognised.
Instead of trying to look at a mugshot of a criminal, like in the real world, the main task should be ensuring that the doors, windows or even chimneys are locked up, to prevent a thief from infiltrating. What if someone at home has accidentally let in a criminal? A cyber security system has to detect this automatically.
With Sophos’ Intercept X, for example, any spontaneous malicious encryption of files would be stopped in its tracks. It would even roll back any encrypted files to the original states. This automation saves time and money for users.
Just as importantly, a forensic tool allows users to find the root cause of the problem. They can see how a piece of malware got in and scan for any remnants that may still be sticking around, say, in a Windows PC’s registry. Cleaning up is key to avoiding a repeat infection.
Developed as a core component of Sophos’ synchronised security strategy, Sophos Intercept X is enabled with the Security Heartbeat feature to share threat intelligence between the endpoint and the network for a coordinated and automated response to attack.
Just as criminals are getting smarter, enterprises have to get up to speed to counter the new threats. Having the tools to automate tasks and stop an attack as it happens will be crucial to avoid being a victim of a new wave of ransomware attacks.
Find out more about Sophos Intercept X.
Drop by the Sophos booth, 021 at Cloud Expo Asia 2017, for live demonstrations on how Sophos Intercept X stops ransomware.





